| 8:00 – 9:00 AM |
Networking Breakfast |
| 9:00 – 9:15 AM |
Welcome and Introductions
- Jeff Moss, Founder, Black Hat + DEF CON
- Steve Wylie, General Manager, Black Hat
-
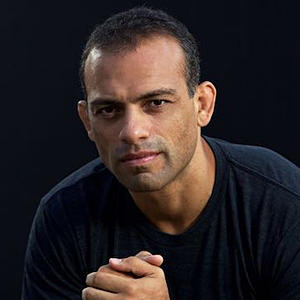
Jeremiah Grossman, MC
Jeremiah Grossman is one of the most-experienced and accomplished experts operating within the internet security realm. He is a specialist at finding network weaknesses and backdoors in order to allow companies to fix them before they’re exploited—or what he calls, a “good hacker.” Jeremiah is currently the Chief of Security Strategy at SentinelOne, a former information security officer at Yahoo!, and the founder of WhiteHat Security, which today boasts one of the largest professional “hacking armies” on the planet. With a career that spans nearly 20 years, Jeremiah has lived a literal lifetime in computer security and has become one of the industry’s biggest names. Coding since he was eight years old, Jeremiah proudly counts breaking software and hardware as “hobbies” and has been publicly thanked by global corporations including Microsoft, Mozilla, Google, Facebook and others for privately informing them of weaknesses in their systems—a polite way of saying, “hacking them.” He grips audiences with his stories of hacking some of the biggest corporations working today and discusses the current threats to secure systems globally, including hacktivists, cyber criminals, and nation states. Jeremiah also shares what businesses need to know to protect themselves now and moving forward as cyber crime businesses using ever-evolving tactics such as ransomware, malware, and economic warfare develop.
Jeremiah began coding at eight and was a network administrator by the time he was 12. At the age of 18, he created a Yahoo! account, hacked into it, and sent instructions on how to do so to Yahoo!’s IT department; he was subsequently offered a job by the tech titan at the age of 18. Jeremiah worked for Yahoo! for several years, managing security for a portfolio of 600 websites in 42 countries with 120 million users. He also worked alongside eBay, Amazon, and even the FBI when the first major DDoS attack occurred in 2000. After leaving Yahoo!, Jeremiah founded WhiteHat, where he worked for 15 years, steadily growing the company until he was ultimately managing a network of 1,000 customers and 30,000 websites.
|
| 9:15 – 9:50 AM |
Cyber War 2022
-
Kenneth Geers
Dr. Kenneth Geers works at Very Good Security. He is an Atlantic Council Cyber Statecraft Initiative Senior Fellow, a NATO Cooperative Cyber Defence Centre of Excellence Ambassador, and a Digital Society Institute-Berlin Affiliate. Kenneth served for twenty years in the US Government: in the Army, National Security Agency (NSA), Naval Criminal Investigative Service (NCIS), and NATO. He is the author of "Strategic Cyber Security", editor of "Cyber War in Perspective" and "The Virtual Battlefield", and technical expert to the "Tallinn Manual".
|
| 9:50 – 10:10 AM |
When Your Kinetic War Gets into My Cybernetic Defenses
-
Frank Artes
Francisco Artes is a globally recognized information security executive who has helped form many of the best practices for securing intellectual property within the computer gaming, motion picture, and television industries. Francisco is also known for his work on cybercrime, hacking, and forensic security with various law enforcement agencies such as the US Dept. of Homeland Security, FBI, Texas Rangers, Europol, and US Marshals. He holds several patents on malware sampling and security vulnerability modeling, has authored numerous white papers and academic papers in the field, and has been a keynote speaker at security conference around the world.
|
| 10:10 - 10:30 AM |
Networking Break |
| 10:30 – 11:00 AM |
Building (Zero) Trust Starts with HardFirmware
-
Yuriy Bulygin
Yuriy Bulygin is the CEO and founder of Eclypsium, the Enterprise Firmware Security company. Eclypsium's award winning, cloud-based platform identifies, verifies, and fortifies firmware in enterprise hardware infrastructure: in laptops, servers, network gear, and connected devices. The Eclypsium platform secures your hardware supply chain by monitoring devices for firmware threats, critical risks, and patching firmware across the entire hardware fleet. Prior to Eclypsium, Yuriy was Chief Threat Researcher and led the Advanced Threat Research team at Intel Security, and the Microprocessor Security Analysis team at Intel Corporation. Yuriy is also the creator of CHIPSEC, the popular open-source firmware and hardware supply chain security assessment framework.
|
| 11:00 – 11:30 AM |
Why Cybersecurity is a Key Pillar of ESG: What this means to you as a CISO
-
Joanna Burkey
Joanna Burkey is the Chief Information Security Officer at HP. In this role, Joanna and her team have responsibility for HP’s global cybersecurity program, including the protection of infrastructure, technology platforms, and business units. Her organization has responsibility for identity, governance/compliance, security operations, strategy/architecture and business alignment.
Joanna Burkey is an independent director at ReliabilityFirst, a member of the California-Israel Chamber of Commerce Cybersecurity Board, and a fellow with the Center for Strategic and International Studies in Washington DC. She holds an NACD Directorship Certification from the National Association of Corporate Directors and has a computer science/mathematics background from The University of Texas at Austin and Angelo State University. She has focused on cybersecurity throughout her career. Her previous roles have included software engineering, product strategy, and security evangelism. Joanna is based in Austin, Texas.
|
| 11:30 AM – 12:00 PM |
People Shortage? Skills Gap
-
Dave Kennedy
David Kennedy is founder of Binary Defense and TrustedSec. Both organizations focus on the betterment of the security industry. David also served as a board of director for the ISC2 organization. David was the former CSO for a Diebold Incorporated where he ran the entire INFOSEC program. David is a co-author of the book "Metasploit: The Penetration Testers Guide", the creator of the Social-Engineer Toolkit (SET), Artillery, Unicorn, PenTesters Framework, and several popular open-source tools. David has been interviewed by several news organizations including CNN, Fox News, MSNBC, CNBC, Katie Couric, and BBC World News. David is the co-host of the social-engineer podcast and on several additional podcasts. David has testified in front of Congress on two occasions on the security around government websites. David is one of the founding authors of the Penetration Testing Execution Standard (PTES); a framework designed to fix the penetration testing industry. David was the co-founder of DerbyCon, a large-scale conference started in Louisville, Kentucky. Prior to the private sector, David worked for the United States Marine Corps and deployed to Iraq twice for intelligence related missions.
|
| 12:00 - 1:30 PM |
Lunch |
| 1:35 – 2:10 PM |
Cyber Insurance – The Current State and ways to Influence the Future
-
Kirsten Bay
Kirsten Bay brings more than 25 years of experience in risk intelligence, information management, and policy expertise across a variety of sectors with the last 6 years as a CEO for technology companies.
Throughout her career, Kirsten has been appointed to congressional committees developing cyber policies, initiatives and recommendations for the intelligence community. She has developed recommendations in partnership with the Center for North American Studies (CNAS) and Center for Strategic and International Studies(CSIS) for The White House energy policy, and collaborated on information studies for MIT-Harvard and several federal agencies. She has gone before a parliamentary subcommittee on recreating trust in the global economy, presented national security and critical infrastructure concepts at conferences such as Black Hat, Secured Americas, Enterprise Architecture Institute, SC World Congress, and the Eurim Information Management Committee. She has also spoken on applied economics and its relationship to both cyber and national security around the world.
In previous executive roles for Cyber adAPT, ISC8, Attensity Group, and iSIGHT Partners, she has led companies through corporate restructuring, risk and corporate intelligence product launches, and company turnarounds.
|
| 2:10 – 2:45 PM |
Unifying Asset, Attack Surface, and Vulnerability Management
-
Daniel Miessler
Daniel Miessler is a recognized cybersecurity expert and writer with 20 years in Information Security. His experience ranges from technical assessment and implementation, to executive level advisory services consulting, to building and running industry-leading security programs.
|
| 2:45 - 3:15 PM |
Networking Break |
| 3:15 – 3:50 PM |
The Future of Decentralized Security, from Bug Bounties to Virtual Citizen Armies
-
Alex Romero
Alexander Romero has an ethos of breaking devices in order to understand hidden inner workings. He enjoys pushing the limits of technology to see how it fails in order to make it better, stronger, and more resilient.
|
| 3:50 – 4:25 PM |
The Great (Cyber) Resignation – Defense in Depth for Keeping/Building Your Teams
-
Jason Haddix
Jason Haddix currently serves as the Head of Global Cyber Security for Ubisoft where he leads all efforts in cyber security. His group protects over 22,000 employees worldwide with a vast scope. In previous roles Jason was Director of Penetration Testing at HP, leading all efforts on matters of information security consulting. Jason has also served as a Director of Operations and VP of Trust and Security at Bugcrowd, leading teams of highly technical Application Security Engineers and Technical Operations staff. While leading teams for the past 11 years, Jason is also a world renowned security engineer and hacker, participating in the bug bounty scene and releasing methodologies and tools for ethical hackers.
|
| 4:25 – 4:55 PM |
Advisory Panel Lock Note
-
Wendy Nather
Wendy Nather leads the Advisory CISO team at Cisco. She was previously the Research Director at the Retail ISAC, and Research Director of the Information Security Practice at 451 Research. Wendy led IT security for the EMEA region of the investment banking division of Swiss Bank Corporation (now UBS) and served as CISO of the Texas Education Agency. She was inducted into the Infosecurity Europe Hall of Fame in 2021. Wendy serves on the advisory board for Sightline Security. She is a Senior Fellow at the Atlantic Council’s Cyber Statecraft Initiative, as well as a Senior Cybersecurity Fellow at the Robert Strauss Center for International Security and Law at the University of Texas at Austin.
-
Saša Zdjelar
Saša Zdjelar is the SVP of Enterprise Security at Salesforce where he leads a global organization and is the executive sponsor for strategic corporate security initiatives such as Zero Trust. Prior to Salesforce, Saša spent nearly two decades working in the Energy sector in various security and non-security roles working on strategy, enterprise security & architecture, software engineering, ERP systems designs/integration, program and product management, planning & stewardship, etc.
He is a member of the Forbes Technology Council, a Fellow at the Cyber Readiness Institute (CRI), a member of the Black Hat CISO Summit Advisory Board and BlackHat Content Review board, an active member in organizations such as Infragard, ISACA and ISSA, has been published in various industry publications, and has spoken at a number of industry conferences and universities. Saša holds a Bachelor's degree in Management and Master's degree in Decision Science from the University of Florida.
-
Justine Bone
Justine Bone is a CEO, Board Member and former CISO with 20 years of experience across the medtech, defense, and financial industries. Her broad areas of expertise include technology risk management, business and product development, cybersecurity communications and business development for technology providers. Justine currently holds the position of CEO of MedSec, where she develops cybersecurity program strategies and solutions for Healthcare Delivery Organizations and Medical Device Manufacturers. She also serves as a member of HP Inc.'s Security Advisory Board, is a faculty member of IANS, and is Chairperson of the non-profit Miami Children Corporation. Prior to her current roles Justine led as CEO of Immunity Inc (acquired by Cyxtera) and Chief Information Security Officer and Head of Infrastructure and Risk Management with Bloomberg L.P. and Dow Jones. Justine's training was as a researcher and security analyst for New Zealand's Government Communications Security Bureau.
-
Trey Ford
Trey Ford is a strategic advisor to enterprise leaders and corporate directors. Today Trey serves as Executive Director of Cyber Security in Vista Equity Partners’ Consulting Group. With twenty years focused on the offensive, defensive, and programmatic leadership aspects of security, he is well grounded in public cloud, abuse, application, network, and platform security.
Previously Trey was CISO of the Heroku platform at Salesforce, General Manager of Black Hat, held strategic advisory and global consulting roles, and still apologizes for time served as an auditor.
|
| 4:55 - 5:00 PM |
Closing Remarks |
| 5:00 – 6:00 PM |
Cocktail Reception |